Updated on GitHub 4 months ago (see history)
How to create encrypted paper backup
Requirements
- Adafruit PiTFT monitor (optional)
- Compatible USB webcam (720P or 1080P, powered directly by Raspberry Pi)
- USB keyboard (Raspberry Pi keyboard and hub recommended)
- USB flash drive (faster is better)
- macOS computer
Caveats
- When copy/pasting commands that start with
$, strip out$as this character is not part of the command
Setup guide
Step 1: log in to Raspberry Pi
Heads-up: replace
10.0.1.94with IP of Raspberry Pi.
Step 2: configure console font
Step 3: configure keyboard layout
Heads-up: following instructions are for Raspberry Pi keyboard (US model).
Heads-up: when asked to reboot, select “No” and press enter.
Select “Localisation Options”, then “Keyboard”, then “Generic 105-key PC (intl.)”, then “Other”, then “English (US)”, then “English (US)”, then “The default for the keyboard layout”, then “No compose key” and, finally, select “Finish”.
Step 4: install dependencies
Step 5: install ckcc (used to manage COLDCARD devices, see docs)
Step 6: install mnemonic (used to create and validate BIP39 mnemonics)
Step 7: install passphraseme (used to create passphrases using EFF wordlists)
Step 8: install sss-cli from source (used to split and join secrets using Shamir Secret Sharing)
Install Rust
Heads-up: when asked for installation option, select “Proceed with installation (default)”.
Install sss-cli
Step 9: install trezorctl (used to manage Trezor devices, see docs)
Step 10: install qrcode (used to create QR codes)
Step 11: import Sun’s PGP public key (used to verify downloads below)
imported: 1
👍
Step 12: verify integrity of Sun’s PGP public key (learn how here)
Fingerprint matches published fingerprints
👍
Step 13: download and verify create-bip39-mnemonic.py
Good signature
👍
Step 14: download and verify validate-bip39-mnemonic.py
Good signature
👍
Step 15: download and verify tmux-buttons.py
Good signature
👍
Step 16: download and verify qr-backup.sh
Good signature
👍
Step 17: download and verify qr-restore.sh
Good signature
👍
Step 18: download and verify qr-clone.sh
Good signature
👍
Step 19: download and verify secure-erase.sh
Good signature
👍
Step 20: download and verify trezor-verify-integrity.sh (used to verify integrity of Trezor devices)
Good signature
👍
Step 21: download and verify trezor-restore.sh (used to restore Trezor devices)
Good signature
👍
Step 22: download and verify update.sh
Good signature
👍
Step 23 (optional): install Adafruit PiTFT monitor drivers and disable console auto login
Install Adafruit PiTFT monitor drivers
Heads-up: don’t worry about
PITFT Failed to disable unit: Unit file fbcp.service does not exist..
Disable console auto login
Heads-up: when asked to reboot, select “No” and press enter.
Select “System Options”, then “Boot / Auto Login”, then “Console” and, finally, select “Finish”.
Step 24: make filesystem read-only
Heads-up: shout-out to Nico Kaiser for his amazing guide on how to configure a read-only Raspberry Pi.
Disable fake-hwclock and logrotate
Link /etc/console-setup to /tmp/console-setup
Link /home/pi/.gnupg to /tmp/pi/.gnupg
Enable tmp.mount
Edit /boot/cmdline.txt
Edit /etc/fstab
Step 25: disable networking and “fix” rfkill bug
Step 26: disable Wi-Fi
Heads-up: use
cat /boot/config.txt | grep "dtoverlay=disable-wifi" && echo "Wi-Fi disabled"to see if Wi-Fi is already disabled.
Step 27: delete macOS hidden files (if present)
Step 28: unplug network cable (if using ethernet) and reboot
WARNING: DO NOT CONNECT RASPBERRY PI TO NETWORK EVER AGAIN WITHOUT REINSTALLING RASPBERRY PI OS FIRST (DEVICE IS NOW “READ-ONLY” AND “COLD”).
Step 29 (optional): disable auto-mount of boot volume (on macOS)
Heads-up: done to prevent macOS from writing hidden files to
bootvolume which would invalidate stored SHA512 hash of microSD card.
Enable read-only mode using switch on microSD to SD adapter
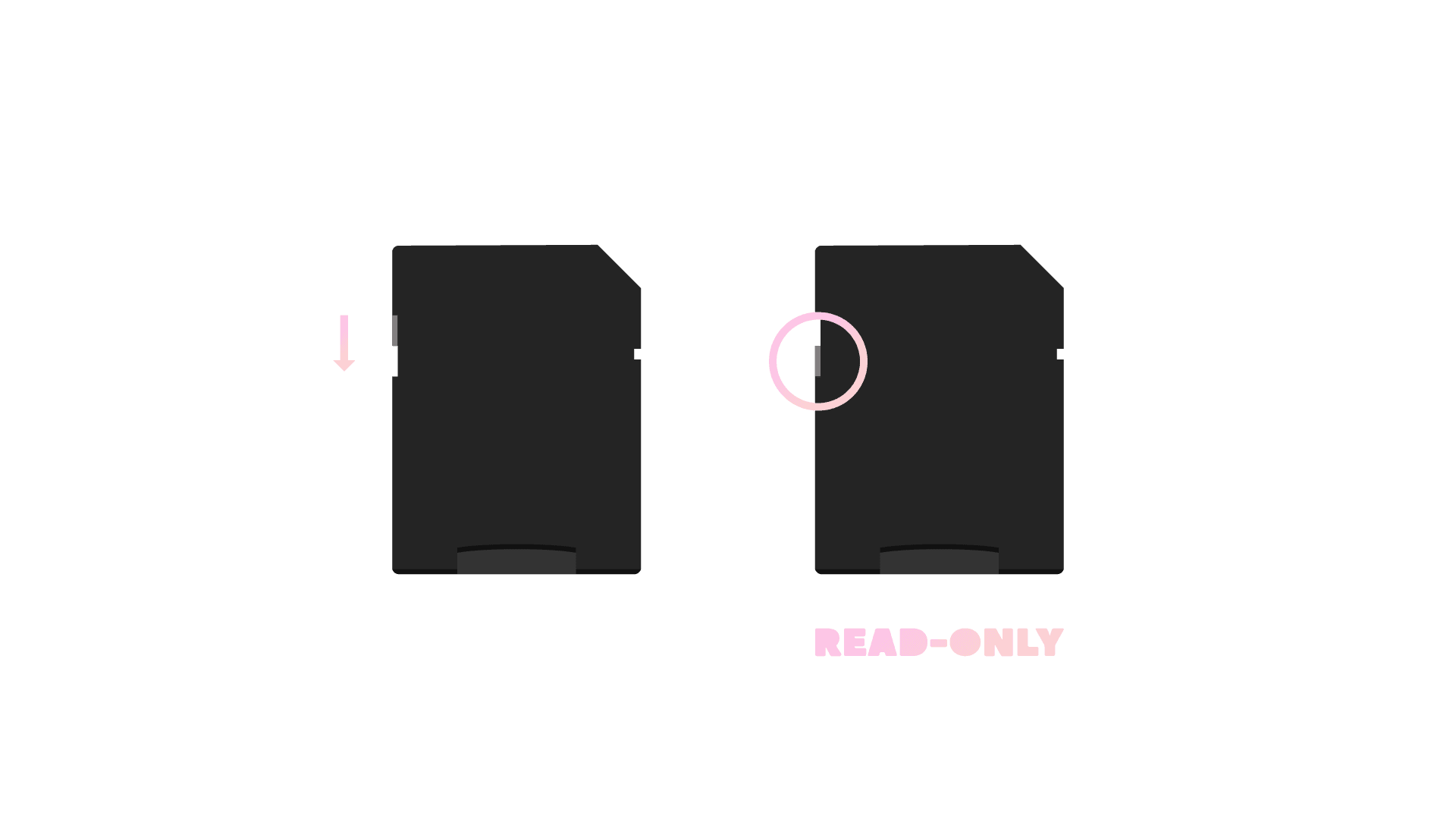
Insert microSD card into adapter and adapter into computer
Run following and eject microSD card
Step 30 (optional): compute SHA512 hash of microSD card and store in password manager (on macOS)
Heads-up: run
diskutil listto find disk ID of microSD card with “Raspberry Pi OS Lite” installed (disk4in the following example).
Heads-up: replace
disknandrdisknwith disk ID of microSD card (disk4andrdisk4in the following example).
👍
Usage guide
Create encrypted paper backup
Done
👍
The following image is now available on USB flash drive.

Restore encrypted paper backup
Heads-up: use
--word-listto split secret into word list.
Done
👍
Clone encrypted paper backup
Done
👍
The following image is now available on USB flash drive.

Secure erase flash drive
Done
👍
